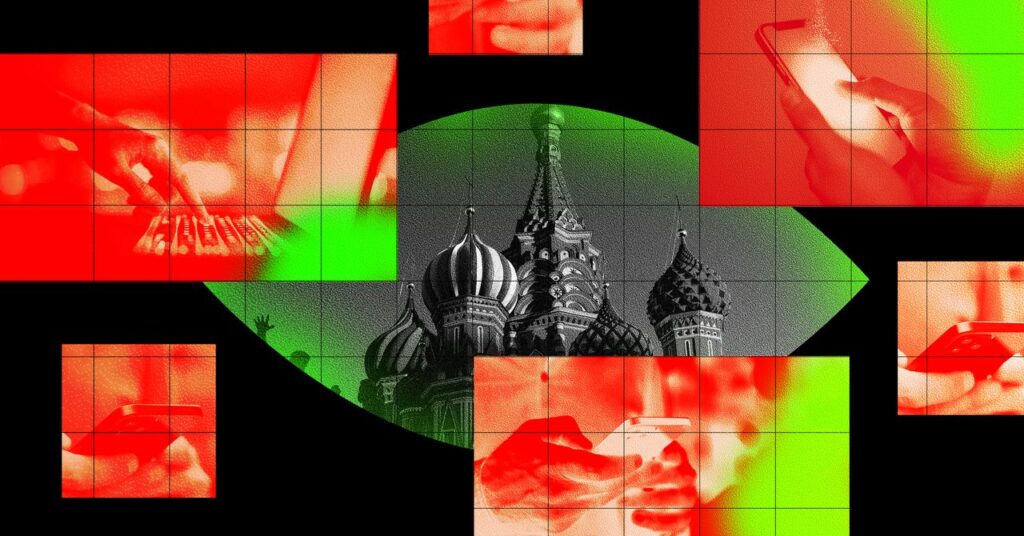
The Russian state hacker group often known as Turla has carried out among the most modern hacking feats within the historical past of cyberespionage, hiding their malware’s communications in satellite connections or hijacking other hackers’ operations to cloak their own data extraction. After they’re working on their residence turf, nevertheless, it seems they’ve tried an equally exceptional, if extra easy, strategy: They seem to have used their management of Russia’s web service suppliers to immediately plant spy ware on the computer systems of their targets in Moscow.
A Microsoft safety analysis workforce targeted on hacking threats at present printed a report detailing an insidious new spy approach utilized by Turla, which is believed to be a part of the Kremlin’s FSB intelligence company. The group, which is often known as Snake, Venomous Bear, or Microsoft’s personal title, Secret Blizzard, seems to have used its state-sanctioned entry to Russian ISPs to meddle with web visitors and trick victims working in overseas embassies working in Moscow into putting in the group’s malicious software program on their PCs. That spy ware then disabled encryption on these targets’ machines in order that information they transmitted throughout the web remained unencrypted, leaving their communications and credentials like usernames and passwords totally weak to surveillance by those self same ISPs—and any state surveillance company with which they cooperate.
Sherrod DeGrippo, Microsoft’s director of risk intelligence technique, says the approach represents a uncommon mix of focused hacking for espionage and governments’ older, extra passive strategy to mass surveillance, through which spy companies accumulate and sift by way of the information of ISPs and telecoms to surveil targets. “This blurs the boundary between passive surveillance and precise intrusion,” DeGrippo says.
For this explicit group of FSB hackers, DeGrippo provides, it additionally suggests a strong new weapon of their arsenal for concentrating on anybody inside Russia’s borders. “It probably reveals how they consider Russia-based telecom infrastructure as a part of their software equipment,” she says.
In accordance with Microsoft’s researchers, Turla’s approach exploits a sure net request browsers make once they encounter a “captive portal,” the home windows which might be mostly used to gate-keep web entry in settings like airports, airplanes, or cafés, but in addition inside some corporations and authorities companies. In Home windows, these captive portals attain out to a sure Microsoft web site to test that the consumer’s laptop is in reality on-line. (It isn’t clear whether or not the captive portals used to hack Turla’s victims had been in reality legit ones routinely utilized by the goal embassies or ones that Turla someway imposed on customers as a part of its hacking approach.)
By benefiting from its management of the ISPs that join sure overseas embassy staffers to the web, Turla was in a position to redirect targets in order that they noticed an error message that prompted them to obtain an replace to their browser’s cryptographic certificates earlier than they might entry the net. When an unsuspecting consumer agreed, they as a substitute put in a chunk of malware that Microsoft calls ApolloShadow, which is disguised—considerably inexplicably—as a Kaspersky safety replace.
That ApolloShadow malware would then basically disable the browser’s encryption, silently stripping away cryptographic protections for all net information the pc transmits and receives. That comparatively easy certificates tampering was doubtless supposed to be more durable to detect than a full-featured piece of spy ware, DeGrippo says, whereas reaching the identical end result.